NightBeacon Platform
Security Operations, Accelerated.
Average attacker breakout time is now 29 minutes. In some cases, 27 seconds. Manual defense can't win that race.
If you've spent any real time in the security trenches, you know the real enemy isn't just ransomware gangs, nation-state hackers, or relentless botnets. It's the endless grind of spreadsheets, metrics, and boardroom battles. For years, we've marched into those meetings armed with hypotheticals: "Here's what didn't happen because we stopped it." When everything runs smoothly, we're invisible heroes. But let one breach slip through, and suddenly everyone's asking why you didn't prevent it. It's a no-win scenario, and it's exhausting.
The core issue is scale. Attackers have mastered automation, deploying AI-driven tools to probe, exploit, and pivot at machine speed. Defenders, meanwhile, have traditionally scaled by throwing more bodies at the problem. Hire more analysts, build bigger teams. But that's a losing game. Alert volumes are exploding exponentially while the pool of seasoned security pros remains frustratingly finite. We're outnumbered, outpaced, and often outgunned.
Let's get into the numbers. "Breakout time" is the critical window from initial access to lateral movement, when attackers start spreading across your network. According to CrowdStrike's latest reporting, average breakout times plummeted to just 29 minutes in 2025, a staggering 65% drop from 2024's already tight 83 minutes. In extreme cases, adversaries achieved lateral movement in as little as 27 seconds, with data exfiltration kicking off in under four minutes.
This compression is being fueled by AI supercharging offensive operations: an 89% surge in AI-enabled attacks, including prompt injections into generative tools for credential theft, LLM-powered malware for automated reconnaissance, and AI-generated scripts for rapid credential dumping. State actors like Russia's Fancy Bear and North Korea's Famous Chollima are leveraging AI to scale their operations, turning enterprise AI systems into prime targets. As CrowdStrike CEO George Kurtz put it: "As AI embeds into workflows, it becomes part of the attack surface. Exploitation follows innovation."
For defenders, this means response windows are disappearing. Every second counts in enrichment, correlation, and investigation. Traditional manual processes are bottlenecks in a high-velocity threat landscape, and if you're still relying on them exclusively, you're already behind.
Look, AI brings real risks and I'm not going to sugarcoat that. Prompt injection can hijack models to output malicious code. Data leakage exposes sensitive information. Model poisoning corrupts outputs with adversarial inputs. And generative AI can absolutely be weaponized for phishing at scale. These aren't hypotheticals. They demand serious engineering discipline: input sanitization, red-teaming models, secure fine-tuning, and runtime monitoring.
But burying your head in the sand isn't risk mitigation. It's surrender. Refusing AI adoption hands attackers a decisive advantage. The data backs this up. Research on generative AI in security operations centers shows real, measurable gains.
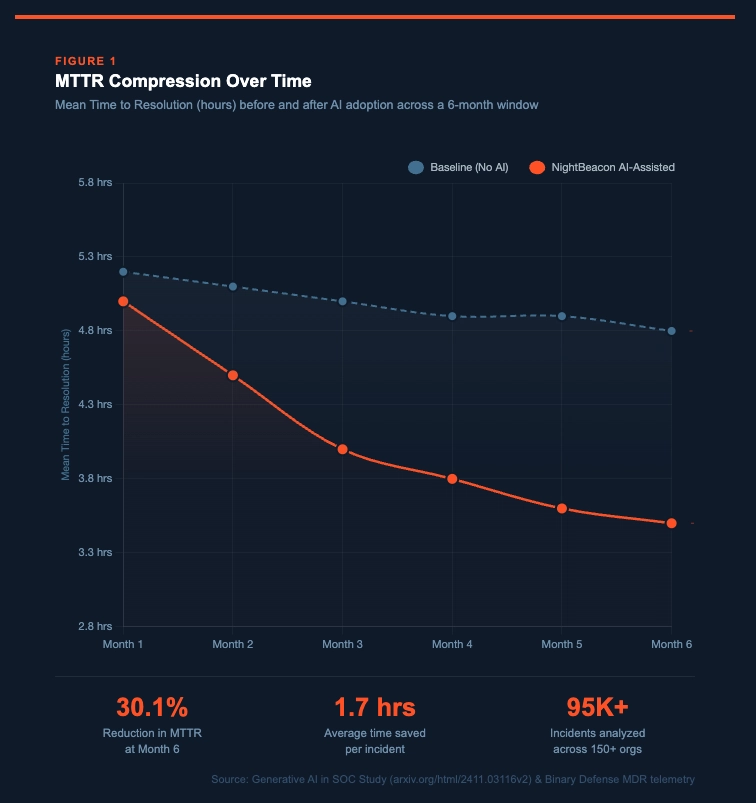
A study on generative AI in SOCs using Microsoft Security Copilot found a 30.13% reduction in mean time to resolution three months post-adoption, based on telemetry from over 150 organizations and more than 95,000 incidents. The gains weren't instant, which tells us there's a learning curve, but they compounded significantly over time.
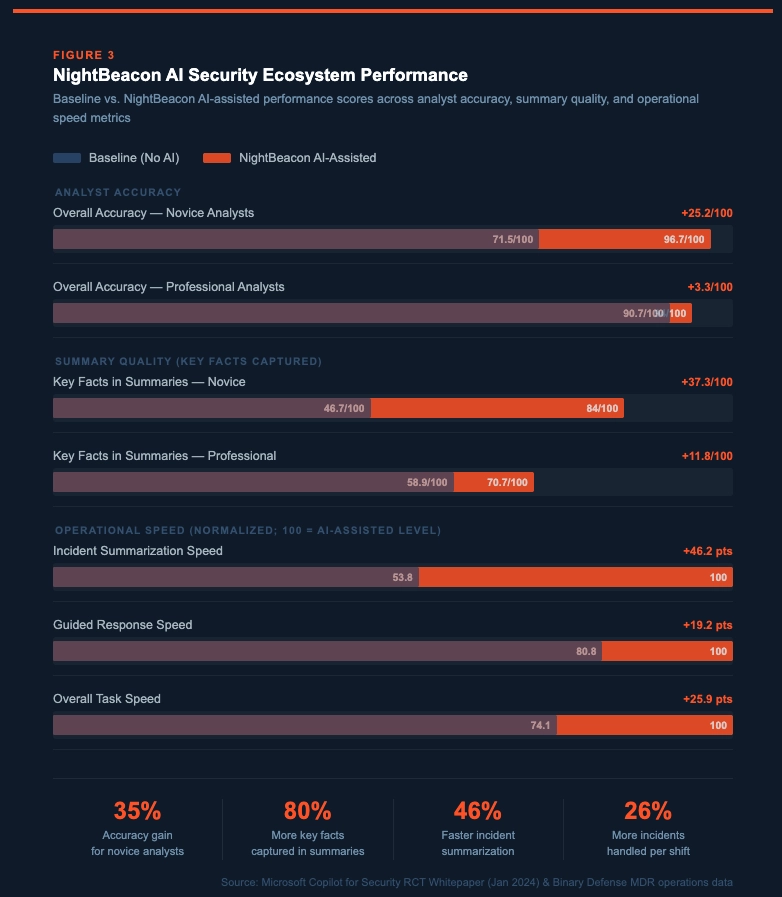
Microsoft's own Randomized Controlled Trials on Copilot for Security involved 296 participants across professional and novice analysts. The results were hard to ignore: professionals saw a 7% overall accuracy boost, up to 12% in script analysis, and completed tasks 23.1% faster, with incident summarization improving by 46.2%. Novice analysts saw even more dramatic gains: a 35% accuracy surge, 43% improvement in guided response tasks, and 25.9% overall time savings.
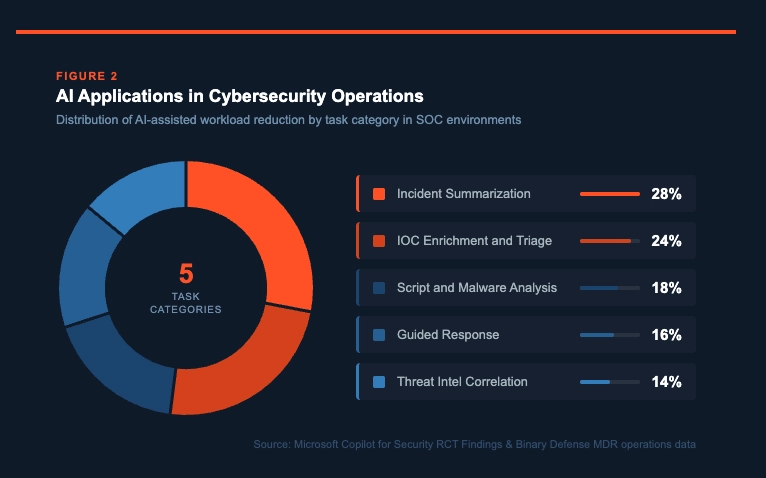
These aren't vanity metrics. Automating incident summaries, script interpretation, and response guidance reduces cognitive load and lets analysts focus on the high-judgment work that actually requires a human brain. AI doesn't replace that. It amplifies it.
At Binary Defense, we've channeled this into NightBeacon, our LLM-driven platform built for rapid AI deployment in SOCs. Built on the ethos of "Outthink. Outsmart. Outlast," NightBeacon is fine-tuned on real-world analyst behaviors, decision trees, and threat patterns drawn directly from our MDR operations.
It's a multi-modal system under the hood. The Enrichment Engine uses natural language processing to query threat intel feeds like VirusTotal and OTX, correlating signals such as anomalous API calls or beaconing C2 traffic. It can parse a suspicious domain's WHOIS data, cross-reference it against known IOCs, and score reputation using ensemble ML models. The Contextual Analysis layer uses transformer-based models to detect linguistic patterns in phishing: urgency tones, grammatical anomalies, homoglyph attacks mimicking legitimate domains. It also assists in reverse engineering by deobfuscating malware, identifying packer signatures, and simulating execution paths via symbolic execution tools integrated directly with the LLM. And everything it outputs comes with confidence rankings and explainability, probabilistic verdicts with traceable reasoning, so analysts always retain veto power.
NightBeacon isn't about replacing humans. It's about multiplying them. It captures collective expertise from our threat hunters and turns chat threads and analyst notes into a shared knowledge graph. Deployed through our MDR services, it's battle-tested across industries like manufacturing and healthcare, where downtime costs millions.
By automating repetitive tasks, pulling IOC context, triaging low-fidelity alerts, generating incident summaries, NightBeacon compresses MTTR in ways that matter operationally. Mean Time to Resolution drops from a 4 to 6 hour average per incident to 2.8 to 4.2 hours, a 30.13% reduction. Incident summarization time cuts roughly in half, from 20 to 30 minutes down to 10 to 15. Script analysis time improves by 10 to 22%.
Those numbers compound across thousands of alerts. In one Binary Defense deployment, a manufacturing client saw MTTR drop from 5.2 hours to 3.6 hours, averting potential production halts that would have cost far more than the platform itself.
AI doesn't automate jobs. It augments them. By offloading the grunt work, NightBeacon boosts throughput without burning out your team. From Microsoft's RCTs, professionals complete tasks 23.1% faster overall, with incident reports coming in 20.5% faster. Novice analysts hit 25.9% faster overall and 19.2% faster on guided response tasks. At scale, that translates to roughly 24 to 26% more incidents handled per shift without adding headcount.
In practice, Binary Defense clients have seen teams process 35% more high-priority alerts.
Every analyst has strengths and blind spots. Maybe they're sharp on malware analysis but weaker on phishing forensics. NightBeacon levels the playing field by embedding team-wide expertise into the platform itself. Novices get an 80% boost in key fact inclusion during summarization. Professionals see meaningful accuracy gains in complex tasks. Overall accuracy for novice analysts jumped from 7.15 to 9.67 out of 10 in the Microsoft study, a 35% improvement that's the difference between a missed indicator and a contained incident.
This raises the floor across the entire SOC, ensuring consistent outcomes regardless of individual experience levels. In our operations, it means junior analysts perform like veterans, reducing errors and helping them grow faster.
Cyber threats aren't slowing down. They're evolving with AI, and they're doing it faster than most organizations can keep up with. The winners in this fight won't be the organizations with the biggest headcount. They'll be the ones who integrate smartest.
The future of cybersecurity isn't human versus AI. It's human with AI. That's how we scale. That's how we win. If you're ready to multiply your defenses, let's talk. At Binary Defense, we're not just watching the horizon. We're lighting the way.