NightBeacon Platform
Security Operations, Accelerated.
We started at 62% confidence on day one. Within 48 hours, we were at 82%, and the system had done that on its own, without a single rule change or version push. We weren't expecting that pace. Neither was the team watching it happen. That's the short version. Here's what it means for security operations.
Every SOC analyst knows the feeling. The queue is full. The alerts keep coming. And the vast majority of them, sometimes 90% or more, turn out to be nothing. False positives are the silent tax on every security operation. They burn time, erode trust in tooling, and create the exact kind of fatigue that lets real threats slip through.
It's not a people problem. The analysts are good. It's a signal-to-noise problem, and it compounds every time a new tool gets added, a new cloud environment spins up, or the attack surface grows.
We built NightBeacon to end that cycle.
The security industry is not short on products that claim to use AI. But there's a meaningful difference between a product that matches patterns against a static training set and a platform that genuinely learns and adapts in production.
NightBeacon doesn't just classify alerts. It builds an evolving understanding of what's normal, what's suspicious, and what's critical — specific to each environment it operates in. It asks the questions a good analyst would ask: What does this alert mean in this environment? Is this behavior anomalous, or is it a known-good process doing exactly what it's supposed to do? What preceded it? What followed it?
The traditional approach to answering those questions involves weeks of rule tuning, threshold adjustments, and painful trial-and-error. NightBeacon compresses that timeline dramatically, and keeps improving as it processes real-world data.
It does this across the full range of inputs a modern SOC depends on: SIEM platforms, EDR and endpoint tools, cloud security, email security, and network security. Every event is not just flagged but scored, contextualized, and explained.
NightBeacon is built specifically for security operations, not adapted from something else, not layered on top of a product that was already doing something different. That distinction matters when you're trying to solve a problem this specific.
When NightBeacon is deployed into a production environment, the AI engine begins ingesting and analyzing security event data immediately. False positives, the noisy, repetitive alert patterns that dominate most queues, get suppressed. Genuine signals get surfaced with higher confidence scores and clearer context.
Early deployments showed confidence scores climbing from the low 60s to over 80% within the first 48 hours, without manual tuning. The platform adapts to the specific log formats, alert structures, and behavioral baselines of each environment it touches. The same event can mean something very different depending on where it occurs, what preceded it, and what follows it. NightBeacon accounts for that.
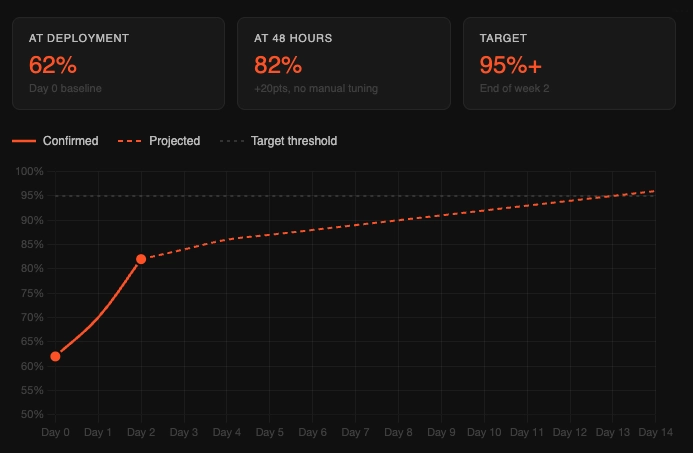
This isn't a one-time calibration. The improvement is continuous. Every environment teaches the platform something. Every analyst interaction sharpens the model.
NightBeacon's effectiveness depends on a loop that doesn't end: the AI learns, humans validate, the AI gets smarter.
SOC analysts are not passengers in this system. Their feedback (what they confirm, what they escalate, what they dismiss) is what accelerates NightBeacon's accuracy over time. That's by design. The goal was never to remove human judgment from security operations. The goal was to make human judgment more effective by removing the noise that buries it.
When the queue is clean, analysts can focus on what actually matters: investigating real threats, understanding adversary behavior, and strengthening defenses. The work that's been crowded out by false positives.
Human Instinct. AI Speed.
The impact of reduced alert fatigue isn't just operational, it's cultural. When analysts trust their queue, they work differently. Escalations mean something. Investigations go deeper. The program gets stronger because the team isn't burning cycles on noise.
For security leaders, the value shows up in the metrics that matter: containment times, dwell time, confirmed impact events. Not "how many alerts did we triage" but "how many bad outcomes did we prevent."
That's the framing NightBeacon is built around. Not alert volume. Outcomes.
If your analysts are spending their days chasing noise instead of investigating threats, that's not just an efficiency problem, it's a risk one. The work that matters doesn't get done.
Security will never be perfect. Environments are too complex, threats evolve too fast, and the attack surface never stops growing. The win isn't "nothing ever happens." The win is: when something happens, your team sees it, contains it, and prevents it from becoming something worse.
That's what NightBeacon is built to deliver.