NightBeacon Platform
Security Operations, Accelerated.
Information stealers continue to be one of the most prolific and damaging malware categories facing organizations today. They are fast, lightweight, and purpose-built to siphon credentials, session tokens, and financial data before defenders have time to respond. Phantom Stealer is the latest variant to emerge from this ecosystem, leveraging phishing campaigns to deploy a multi-stage payload that harvests browser credentials, cryptocurrency wallet data, and Discord authentication tokens, then exfiltrates everything over attacker-controlled Telegram, Discord, or FTP channels.
What makes Phantom Stealer particularly noteworthy is its use of living-off-the-land techniques. Rather than relying solely on custom tooling, it abuses legitimate, Microsoft-signed binaries like msedge.exe and cookie_exporter.exe to blend malicious activity into normal system behavior, thus making detection significantly harder for traditional endpoint tools.
ARC Labs researchers analyzed a recent Phantom Stealer sample within the Binary Defense malware lab. This research walks through the full infection chain, details the data harvesting techniques observed, and provides actionable detection guidance to help defenders identify and disrupt Phantom Stealer activity in their environments.
Researchers analyzed a sample of Phantom Stealer in the Binary Defense malware lab to outline the infection chain noted in recent campaigns. The diagram below illustrates the full process flow from initial execution through data exfiltration.
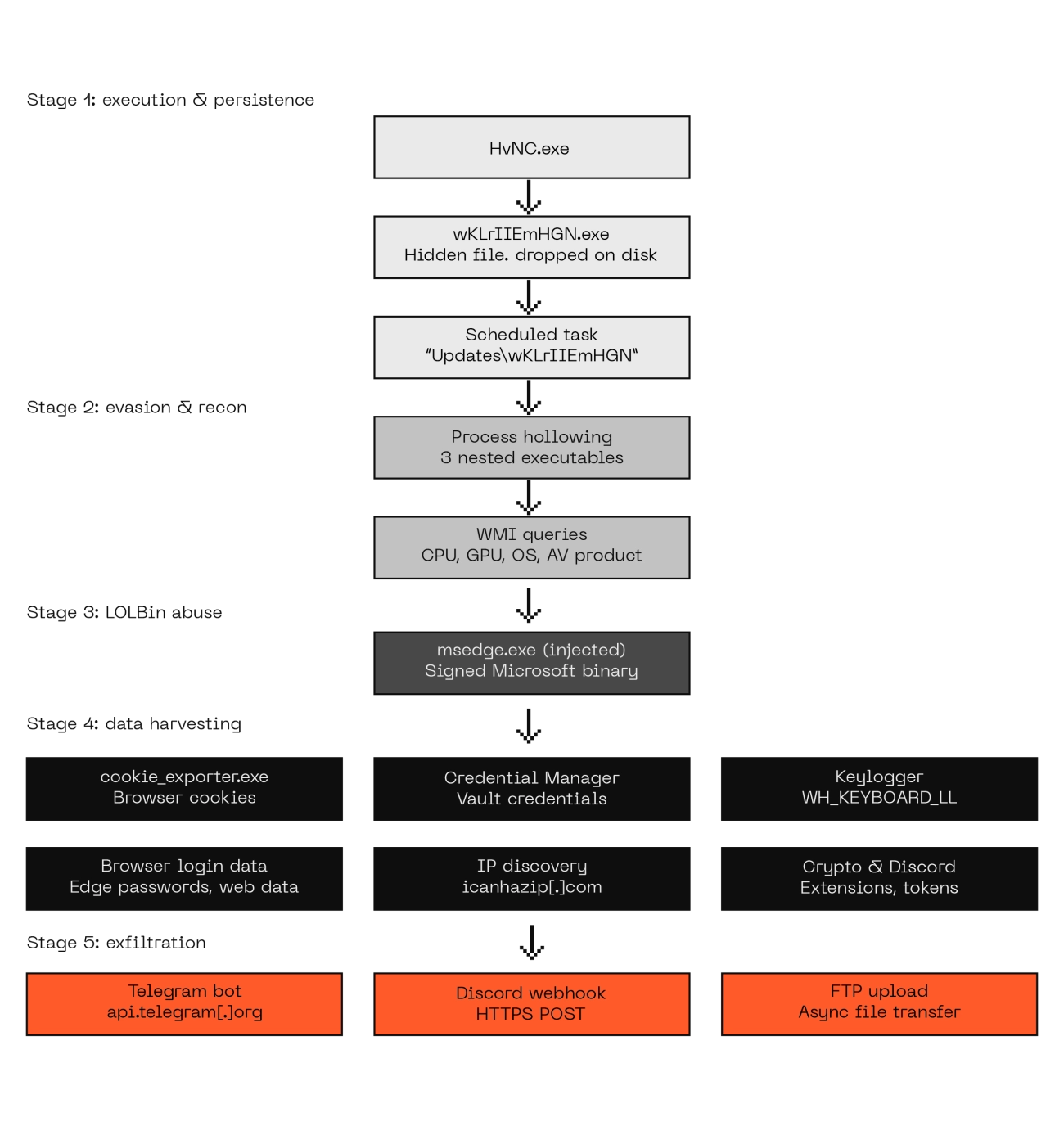
Initial static analysis of the Phantom Stealer payload revealed that the original file name was HvNC.exe. Upon execution, a hidden file titled wKLrllEmHGN.exe was created, followed by a scheduled task creation performed via the following command line:
"schtasks.exe" /Create /TN "Updates\wKLrIlEmHGN" /XML "C:\Users<REDACTED>\AppData\Local\Temp\tmp83A8.tmp"
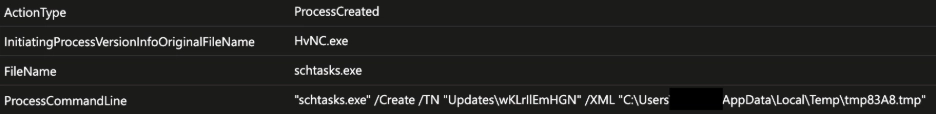
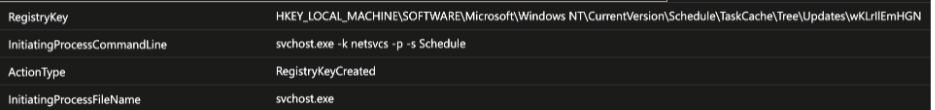
The use of an "Updates" naming convention for the scheduled task is a deliberate social engineering choice, it blends in with legitimate Windows Update tasks and is easy to overlook during triage. The task creation via schtasks.exe automatically generates corresponding registry entries within the HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Schedule\TaskCache\ key. Specifically, the following registry modification was observed:
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Schedule\TaskCache\Tree\Updates\wKLrllEmHGN
The malware then performed process hollowing on itself and relaunched as a child process. This is a significant evasion technique: by hollowing its own process and injecting into the newly created child, Phantom Stealer ensures the malicious code never runs in its original process context. This complicates memory forensics and can bypass security tools that rely on process lineage or image-path validation.
The child process executed the following WMI queries to fingerprint the host’s hardware:
These queries serve a dual purpose: they collect system information for exfiltration and can be used for sandbox detection, since virtual environments often expose identifiable hardware signatures. The child process then dropped an additional copy of Phantom Stealer, resulting in a total of three nested files within the process chain. After this, the process chain repeated the WMI queries above and launched msedge.exe on a non-primary window/desktop via the following command line:
"msedge.exe" --no-sandbox --allow-no-sandbox-job --disable-gpu --mute-audio --disable-audio --user-data-dir="C:\Users<REDACTED>\AppData\Local\Temp\ifkrlxk1.it1" --edge-skip-compat-layer-relaunch
This is the most tactically significant phase of the infection chain. By launching a legitimate, Microsoft-signed copy of msedge.exe with specific command-line flags,including --no-sandbox and a temporary --user-data-dir, Phantom Stealer gains a trusted process context from which to conduct all subsequent data harvesting. Because the binary is legitimately signed, many endpoint detection tools will allow its network and file system activity without scrutiny.
The injected msedge.exe process first enumerated the hosts file on the compromised system. It then spawned an additional process titled cookie_exporter.exe, observed with a SHA256 hash of 77199be2affe524fcfbb223b6eaf5dd9d87ab52150ae75acafa3d3543c80d33e. This is another legitimate, signed Microsoft executable associated with the management and export/import of Microsoft Edge browser cookies, invoked here to harvest saved cookie data from the victim’s browser profile.
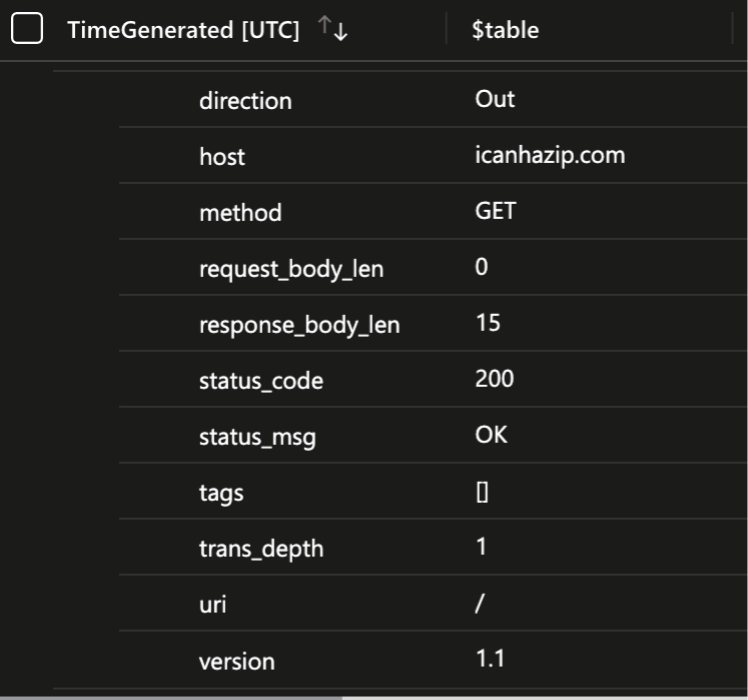
Data harvesting continued with msedge.exe enumerating vault credentials from Credential Manager. Additional WMI queries were executed to gather information about the operating system and the antivirus product installed on the system. The computer’s public IP address was then obtained via an HTTP request to icanhazip[.]com, and a hook titled WH_KEYBOARD_LL was set to capture the compromised user’s keystrokes in real time.
As part of the ongoing cycle of remote thread injection and outbound connections, the infected msedge.exe process also launched identity_helper.exe and setup.exe in a hidden window. These two processes are related to Microsoft Edge installation and user information.
Phantom Stealer then accessed browser login data and web data stored at the following directories:
\Device\HarddiskVolume3\Users<REDACTED>\AppData\Local\Microsoft\Edge\User Data\Default\Login Data
\Device\HarddiskVolume3\Users<REDACTED>\AppData\Local\Microsoft\Edge\User Data\Default\Web Data
Phantom Stealer ships with three exfiltration modules, giving operators built-in redundancy if one channel is blocked or monitored. The table below summarizes each module’s mechanism and the network indicators defenders should monitor.
Module |
Protocol / Mechanism |
Network Signature |
Telegram |
HTTPS to Telegram Bot API |
Outbound HTTPS connections to api.telegram[.]org; async routines send messages, system information, and stolen files to the threat actor’s bot. |
Discord |
HTTPS to Discord Webhook |
Outbound HTTPS POST requests to Discord webhook URLs (discord[.]com/api/webhooks/); collected data sent to attacker-controlled channels. |
FTP |
FTP file upload |
Asynchronous FTP uploads to an attacker-specified server; monitor for unexpected outbound FTP (port 21) or passive FTP data connections. |
The sample analyzed in the Binary Defense malware lab ultimately connected to api.telegram[.]org to exfiltrate stolen data from the compromised system.
The infection chain described above produces several high-fidelity detection opportunities across endpoint telemetry, registry monitoring, and network traffic. The table below maps each stage of the attack to specific observables and recommended data sources for threat hunting.
Stage |
Technique |
Observable |
Data Source |
Persistence |
Scheduled task creation |
schtasks.exe /Create with "Updates\" naming convention; corresponding TaskCache registry writes |
Process creation logs, Registry monitoring |
Evasion |
Process hollowing |
Parent process spawning identical child with hollowed memory; three nested layers of the same payload |
EDR telemetry, Memory forensics |
Reconnaissance |
WMI system fingerprinting |
WMI queries for Win32_Processor and Win32_VideoController from non-standard parent processes |
WMI trace logs, Sysmon Event ID 1 |
Defense evasion |
Signed binary proxy execution |
msedge.exe launched with --no-sandbox flag and temporary --user-data-dir from a non-browser parent |
Process creation logs, Command-line auditing |
Credential access |
Browser credential harvesting |
cookie_exporter.exe spawned by injected msedge.exe; access to Login Data and Web Data SQLite files |
File access auditing, EDR telemetry |
Credential access |
Credential Manager enumeration |
Vault credential reads from injected msedge.exe process context |
Windows Vault/Credential logs |
Collection |
Keylogging |
WH_KEYBOARD_LL hook set from non-standard process |
API monitoring, EDR telemetry |
Discovery |
Public IP lookup |
HTTP GET to icanhazip[.]com or similar IP-echo services |
Network proxy logs, DNS monitoring |
Exfiltration |
C2 over web services |
Outbound HTTPS to api.telegram[.]org, Discord webhook URLs, or unexpected FTP connections |
Network traffic analysis, Firewall logs |
For actionable detection rules and threat hunting queries, check out the ARC Labs GitHub repository.
https://thehackernews.com/2025/12/phantom-stealer-spread-by-iso-phishing.html